Infrastructure Intelligence: Exploit your adversary’s Achilles’ heel
Regardless of how an attacker breaches the network or how fraud is committed, there is always the use of Internet infrastructure. As the world’s leading source of infrastructure intelligence, we provide not just advanced detection, protection, and visibility but true proactive resiliency against all forms of digital risk.

Experts in your adversary’s infrastructure
Your adversary utilizes various Internet infrastructure, devices, and assets to conduct their malicious activities. As experts in infrastructure intelligence, HYAS not only sees what they are doing but keeps you one step ahead.
$ 4.88 M
Average cost of a data breach
72 %
Increase in data breaches since 2023
$ 12 T
Projected cost of cyber crime in 2025
$ 10 B
Cost of cyber fraud losses / year
HYAS Products
HYAS security solutions provide the visibility and observability needed to stay in control of your environment. HYAS solutions are easy to deploy, easy to manage, and integrate seamlessly into any security stack.
HYAS Protect
Protective DNS
Our protective DNS solution combines authoritative knowledge of attacker infrastructure and domain-based intelligence to proactively block malicious communication used by cybercriminals to conduct phishing, ransomware, and other forms of cyberattacks.

HYAS Insight
Threat Intelligence & Investigation
HYAS Insights allows you to rapidly discover and investigate any IOC and related indicators. Identify and map out the complete cybercriminal campaign architecture and take a proactive stance against future attacks, fraud, and all forms.
Award-Winning Technology
HYAS is globally recognized for our proactive threat intelligence and investigation platform and advanced protective DNS solution that empower organizations to safeguard against cyberattacks.


/2024%20Award%20Logos/Globee%20Awards%202024%20Gold%20Cybersecurity-82x82.png?width=82&height=82&name=Globee%20Awards%202024%20Gold%20Cybersecurity-82x82.png)

/2023%20Award%20Logos/Top%20infosec%20innovators%20Winner%20PNG-%20Badge-82x82.png?width=82&height=82&name=Top%20infosec%20innovators%20Winner%20PNG-%20Badge-82x82.png)
/2023%20Award%20Logos/SaaS%20CEO-82x82.png?width=82&height=82&name=SaaS%20CEO-82x82.png)

/2023%20Award%20Logos/HYAS%20Network%20Security-82x82.png?width=82&height=82&name=HYAS%20Network%20Security-82x82.png)







/2024%20Award%20Logos/CyberSecurityAward-2024-01_82x82.png?width=82&height=82&name=CyberSecurityAward-2024-01_82x82.png)
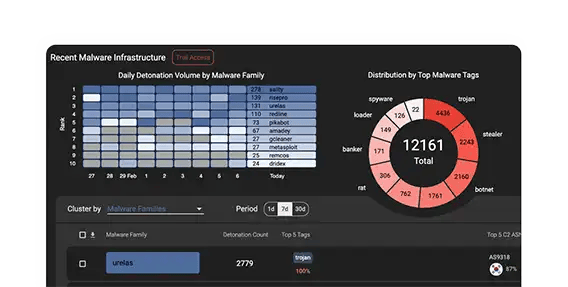
SentinelOne Deploys HYAS for Proactive Security
SentinelOne integrates HYAS Protect into its technology stack to enhance its security posture with a defense-in-depth strategy. HYAS Protect protective DNS solution helps fortify the cybersecurity company’s security hygiene, identifies gaps, and proactively block malicious activities at the DNS layer. This case study explores SentinelOne's use of HYAS Protect to stay ahead of cyber threats and maintain a resilient security posture.
HYAS in Action
HYAS offers SaaS cybersecurity solutions leveraging advanced threat actor infrastructure knowledge to provide proactive threat intelligence and network protection. HYAS combines authoritative knowledge of attacker infrastructure and unrivaled domain-based intelligence to proactively identify, defend and block the command and control (C2) communication used by malware, ransomware, phishing, and other forms of cyberattacks.
HYAS Shines a Light on Financial Fraud
HYAS provided a major national bank unprecedented visibility into the origins of cyberattacks against their institution, including the campaign infrastructure being used, and the architecture likely to be used against it in the future. Serving more than 8.5 million customers in business, retail, and other sectors worldwide, the bank turned to HYAS to protect their highly sensitive data from breaches, malware, fraud, and other cybercrimes.

HYAS Solutions
HYAS empowers organizations with advanced threat intelligence and innovative technologies to proactively identify, investigate, and mitigate cyber threats.

Fraud Investigation
We offer advanced threat intelligence tools and methodologies to detect, investigate, and mitigate fraudulent activities, ensuring robust protection for your digital assets.

Cyber Forensics & Incidents Investigation
Our threat investigation solution is expertly designed to swiftly identify, analyze, and respond to security incidents to safeguard your digital infrastructure against emerging threats.
Threat Hunting
Our threat intelligence and investigation platform enables security teams to proactively leverage advanced analytics and unique data to detect and neutralize potential threats before they compromise your systems.
Hear From HYAS Clients
Employing HYAS Insight has streamlined our investigations with an easy-to-use interface and needed contextual information. One pane of glass usually gives us what we need. HYAS Insight is typically our first pivot point on new investigations.
”HYAS Insight is our go-to resource, enabling us to connect the dots to rapidly investigate and understand threats affecting our clients.
”Everyone has data. It is about context. You need good quality data, but also applying data in a meaningful context. We take the high-quality data that comes from HYAS Protect and together with our proprietary technology, I get the depth, breadth, and context from my data. My team can understand if it is something we expect or don’t expect, allowing for quicker decisions to be made.
”
HYAS has increased our overall productivity for both our company and our security team. We have been very happy partnering with HYAS.
”/portlandleathergoodscom-70x70.jpg?width=70&height=70&name=portlandleathergoodscom-70x70.jpg)
HYAS Protect is an investment in an organization’s future, delivering quantifiable outcomes such as fortified financial defense, customer trust, and compliance confidence. With HYAS, you position your organization for sustainable growth, competitive advantage, and peace of mind in an increasingly threat-filled digital landscape.
”/LOGO_RGB_RSM_US_Color-70x70.jpg?width=70&height=70&name=LOGO_RGB_RSM_US_Color-70x70.jpg)
HYAS Insight is our go-to resource, enabling us to connect the dots to rapidly investigate and understand threats affecting our clients. It is a core investigative tool that supports the core functions of the team which delivers complete threat intelligence to the client.
”The HYAS speed of investigation was incredible. We were blown away by their responsiveness, knowledge, and expertise. To rapidly identify security issues in our infrastructure as well as find the culprits was astounding. HYAS jumped in and located the hacker in hours.
”Latest News & Resources
Securing the Modern Grid: Why Infrastructure Intelligence is Required for Critical Infrastructure
As global tensions rise and the energy sector undergoes rapid digital transformation, the stakes...
Continue ReadingUnpacking the Collins Aerospace Attack: Infrastructure Intelligence Lessons from Aviation Disruption
When most people think about critical infrastructure, they think about power grids, pipelines, or...
Continue ReadingTop 20 Blocked Destination Countries
HYAS blocks tons of queries on behalf of our clients each day and we occasionally step back and...
Continue Reading
Ready to Get Started?
Schedule a consultation with one of our security experts today to learn more, request a personalized demo, and discover how HYAS’ comprehensive, proactive cybersecurity intelligence and threat protection can safeguard your organization.


