Risepro Malware Campaign On the Rise
Posted by David Brunsdon | April 22 2024
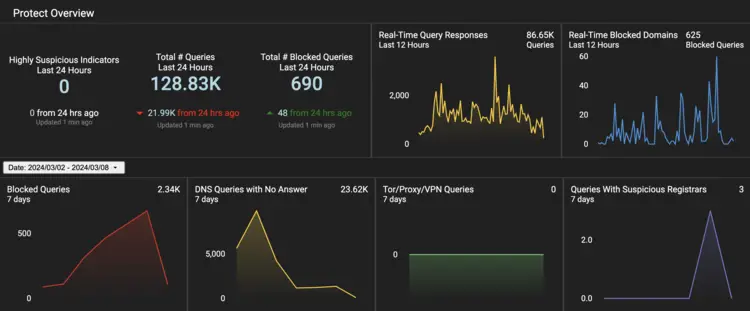
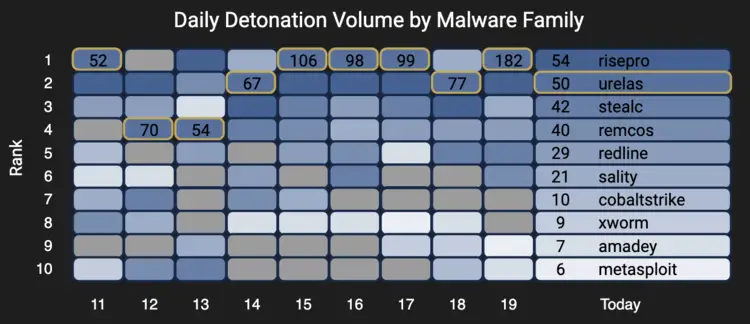
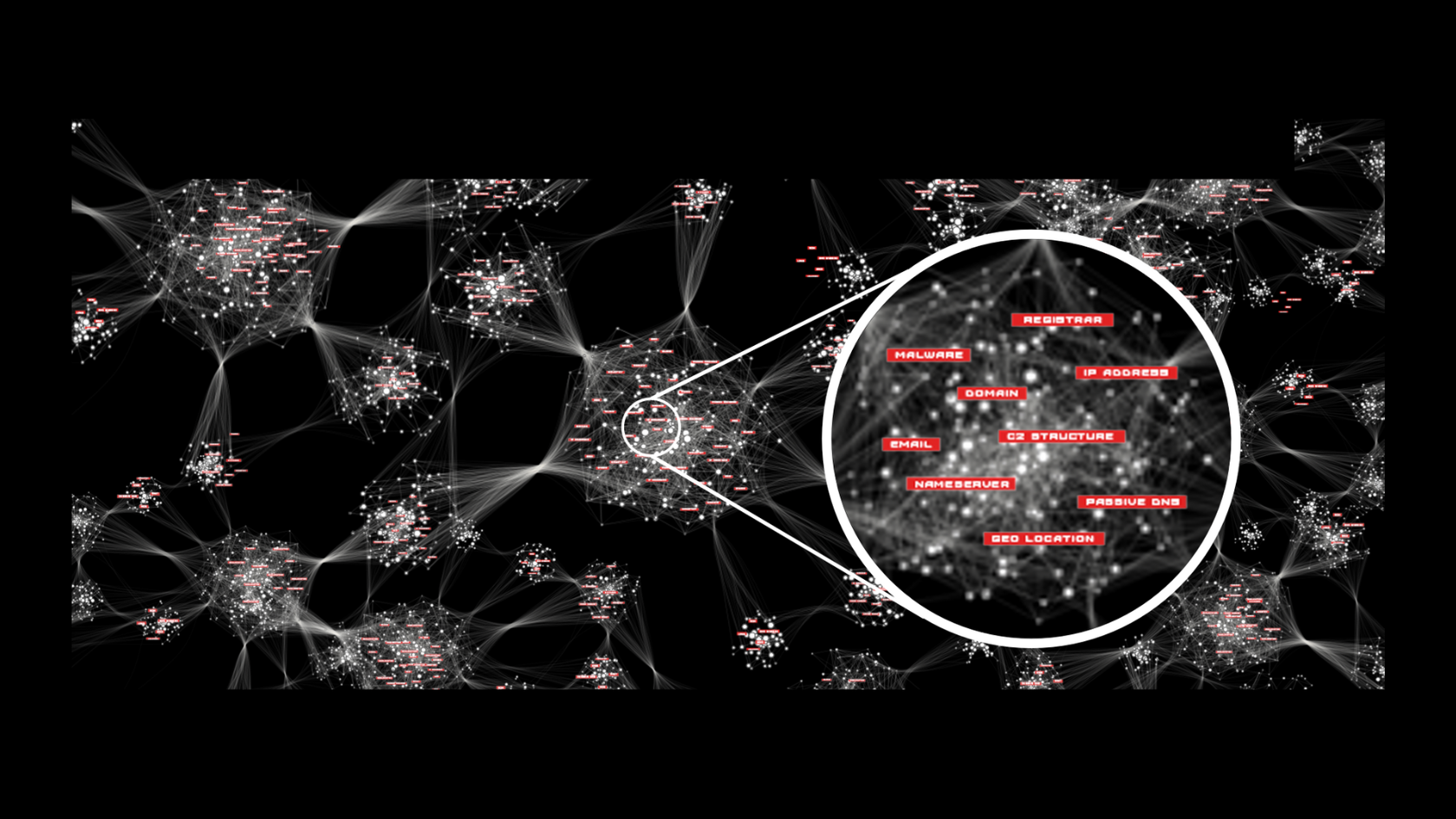
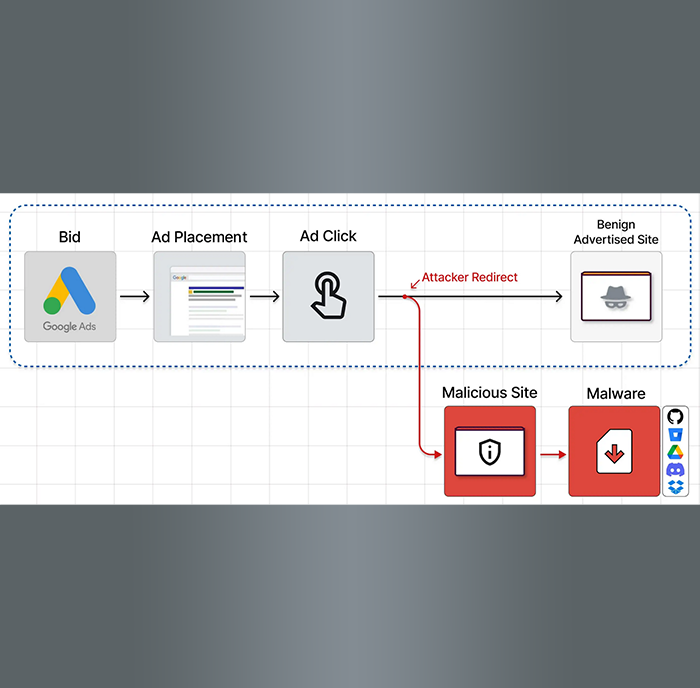
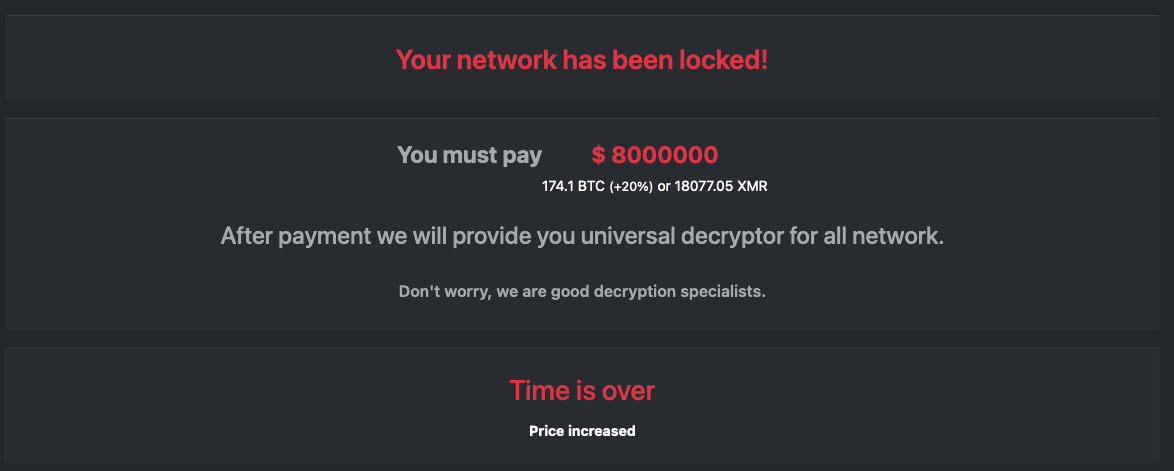
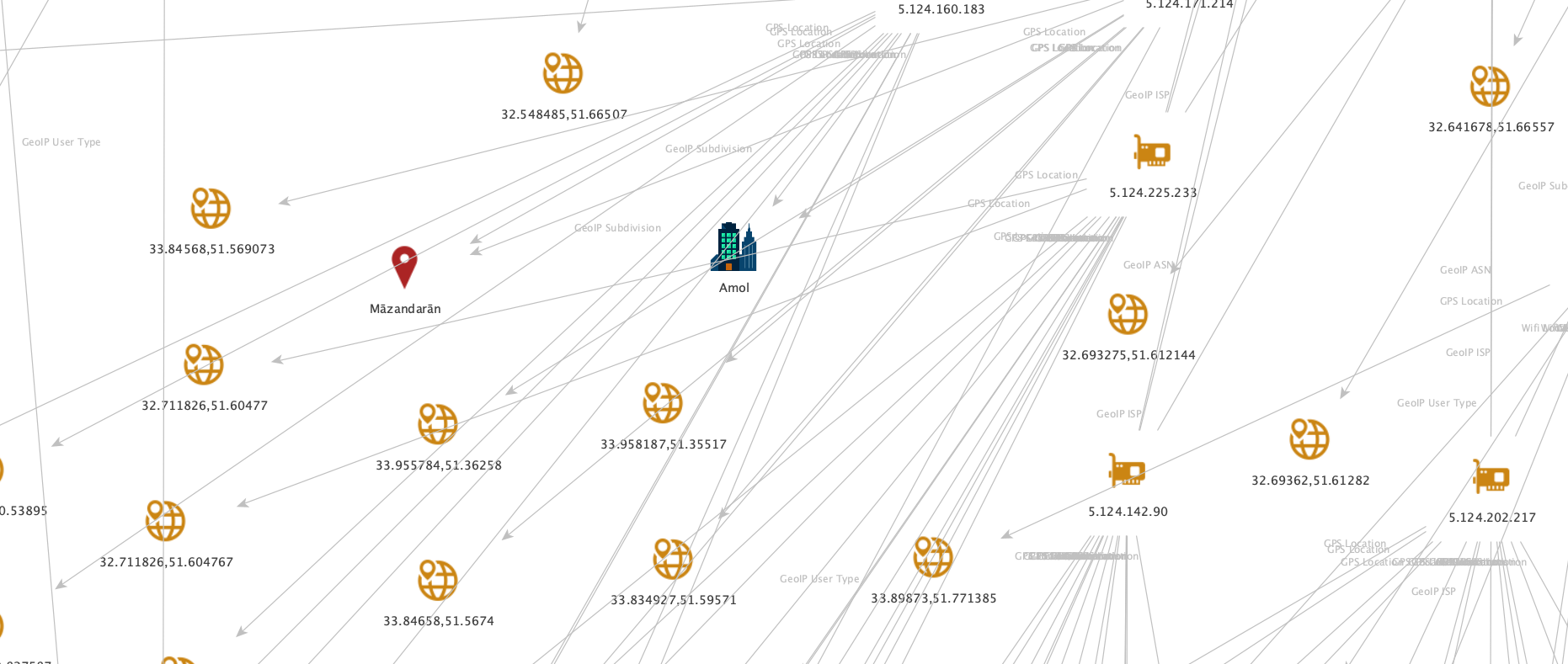
Weekly Threat Intelligence Report Date: April 22, 2024 Prepared by: David Brunsdon, Threat Intelligence - Security Engineer, HYAS I read this article the other day from Hacker News about a DNS-based malware campaign that used fake IP scanners in the industry-news channel. I spent some time looking into it in the HYAS Insight threat intelligence and investigation platform. I was able to uncover the registration details, which led to a google cloud IP that was operating C2 from their email, and then to a potential actor IP in Nigeria. This led me to more exploration, and I am nowhere near done with it, so stay tuned on this! This week, we saw a surge in activity related to the Risepro malware, particularly targeting IP address (((147.45.47.93))) - its C2 “mother ship.” This signifies a concerning development in the cyber threat landscape, as Risepro, akin to StealC, is a notorious form of stealer malware designed to exfiltrate sensitive information from compromised systems. This threat