Threat Reports
New Advanced Phishing Kits Target Digital Platforms
 Posted by HYAS Intel Team | July 10 2019
Posted by HYAS Intel Team | July 10 2019
The difference between an obvious phish and a successful one is often the technical skill and attention to detail of the phish’s author. Gone are the days of poorly designed phishing kits and obvious deception; instead, a number of phishing kit authors are using increasingly sophisticated tactics to evade detection and trick targets into disclosing sensitive information. HYAS Infosec has observed a significant increase in the number of skillfully crafted phishes targeting several industries. One such example includes a phishing campaign against users of Steam, the online gaming and distribution platform developed by Valve Corporation.
Using Steam phishes as an example, this series will explore sophisticated phishing operations in three parts: (1) identifying phishing domains using Comox, HYAS Infosec’s online attribution intelligence platform, (2) technical analysis of advanced phishing techniques and the underlying social engineering tactics that make this phishing campaign so effective, and (3) using the results of our analysis to understand the tactics these bad actors use to deploy, manage, and profit from their phishing operations within the wider underground economy.
Why target Steam accounts?
Steam accounts are appealing targets for several reasons. A successful phishing attack often results in a victim’s digital goods being transferred to an attacker-controlled account where they are then traded or sold. These goods can represent significant investments of time and money, often with little recourse for victims. Hijacked accounts are also sold or rented to other ne’er-do-wells on underground hacking forums. (Indeed, some sellers of hijacked Steam accounts offer guarantees that an account will be accessible for a minimum length of time.) Additionally, a hijacked account can be used to deliver malicious links to other Steam users or be held for ransom, though this tactic is less common.
The hunt begins.
HYAS Infosec monitors several phishing actors that target Steam users across the globe. One domain we found of interest will be where our investigation begins:
ċŝ[.]money (xn--8da8n[.]money)
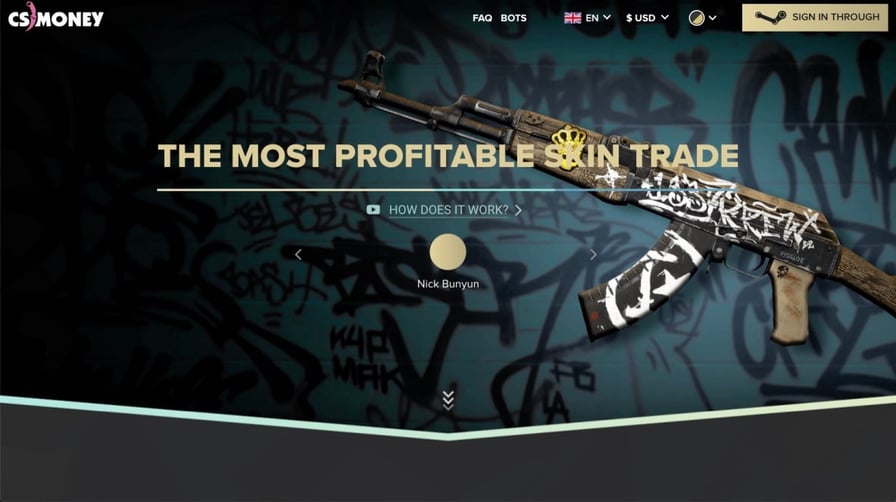
This domain uses an IDN homograph attack to impersonate the legitimate domain cs.money, a digital goods trading platform for gamers. Upon visiting ċŝ[.]money, a user lands on a website resembling cs.money, including the option to log in using a Steam account.
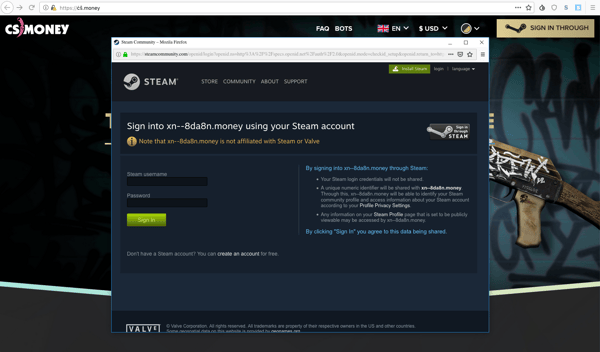
Once a potential victim clicks on the login with Steam button, a fake browser window appears with an equally phony Steam login panel, a technique known as a picture-in-picture attack. In this example, the fake browser window can be repositioned and resized but not moved outside of the browser containing it. Unsuspecting victims believe they are securely logging into cs.money using their Steam accounts. In reality, this is nothing more than a decorated iframe for a phish found on the same domain at ċŝ[.]money/AgBgOTVo/kj71QTLC54uy/. (Part 2 of this series will explore these phishing techniques in detail, including why picture-in-picture attacks are particularly effective against users already aware of phishing threats.)
Request parameters for this phish include: username, password, donotcache, hash, and ref. These parameters are sent via POS
T request to https://huiso[.]su/api/login. Example raw request headers are included below:
Host: huiso[.]su
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://xn--8da8n[.]money/
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Content-Length: 193
Origin: https://xn--8da8n[.]money
Connection: keep-alive
Uncovering additional malicious domains with Comox pivots.
Searching for the domain ċŝ[.]money in Comox reveals a number of potential pivots, including a distinctive name server assigned to this domain. This name server is ns1.anxdns[.]io and has an A record of 5.187.0[.]56. The whois record table in Comox reveals several hundred suspicious domains with similar naming conventions using this name server. Further investigation reveals that these are almost exclusively Steam phishes using the same picture-in-picture attack that was found at ċŝ[.]money. These phishes also send POST requests with identical parameters to huiso[.]su. Further, the domain huiso[.]su uses this very name server.
Next, we pivot in Comox using the name server’s A record to search for additional infrastructure — in particular, name servers that may be assigned to related phishing domains. Using Comox’s passive DNS capabilities, we discover additional name servers using a similar naming convention. These include ns1.anx-dns[.]link and ns1.anx[.]link.
We hit pay dirt. Whois records for both of these name servers reveal more than a thousand additional malicious domains using similar naming conventions. Using Comox, a domain revealed nearly two thousand more malicious ones, allowing researchers to map out a phishing group’s footprint in mere minutes.
Registrant emails:
anonymexx@protonmail[.]com
djack3286@gmail[.]com
o2lsh@1webmail[.]info
tewishave01@gmail[.]com
Name servers:
ns1.anx[.]link
ns1.anx-dns[.]link
ns1.anxdns[.]io
Example domains:
loot-farm[.]com
csgo-up[.]com
cs-leagues[.]com
csgo-leagues[.]com
csgovvinner[.]com
tradeskinsfastx[.]com
Blog Categories
- Blog
- Threat Reports
- HYAS Labs
- Featured
- PDNS
- Threat Intelligence
- Phishing
- DNS Security
- IoT
- Malware
- OT
- Artificial Intelligence
- Attribution
- DNS Tunneling
- Emotet
- Major Attacks
- News
- Research
- flow data
- visibility




